These rights are recorded in a smart contract and the tokens themselves are traded on exchanges. Security tokens are traded in accordance with the legal regulations of various financial regulators, such as the U.S. Securities and Exchange Commission (SEC) or the Swiss Financial Market Supervisory Authority (FINMA).
Morgan Creek Capital Managing Partner Anthony Pompliano, in his article “The Official Guide to Tokenized Securities”, defines security tokens as “digital assets subject to federal securities laws, something in between tokens and traditional financial products. He also refers to security tokens as “programmable property rights” that can be applied to any asset, including public or private capital, monetary obligations, real estate, and so on.
Why do we need security tokens?
Legally, security tokens are treated very differently than so-called utility tokens due to their nature. The latter are popular among ICO organizers as a way for investors to gain access to a company’s product or service. Security tokens, as opposed to utility tokens, are tied to real securities, making them a financial investment, and the companies that issue them are subject to additional regulatory requirements, such as reporting.
Security tokens also address one of the most serious issues with ICOs: the lack of compensation guarantees in the event of project failure or organizer fraud. Furthermore, they can be used to hedge risks in an investment strategy, such as the Simple Agreement for Future Tokens (SAFT). This model is considered safer because it allows accredited investors to purchase tokens after the project’s launch, but it still involves certain risks: investments are made in the promise of receiving tokens in the future, rather than in tokens themselves.
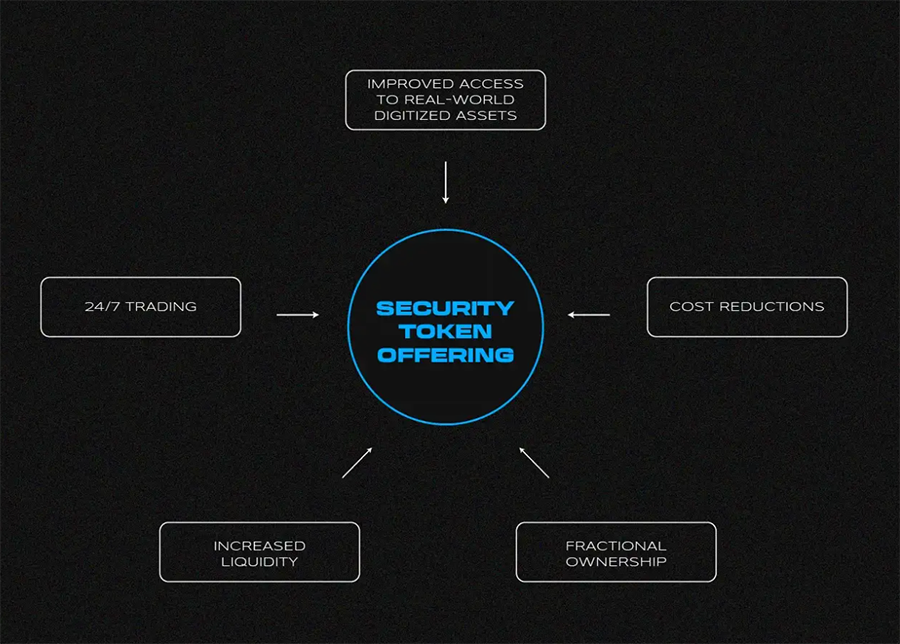
What are the benefits of security tokens?
The elimination of intermediation by banks and other institutions is one of the primary advantages of security tokens over traditional financial products. This creates an entirely new environment for investing and transacting.
Stephen McKeon, a University of Oregon finance professor and the Harbor Project’s adviser (which has raised $28 million in investments to create a protocol for issuing and trading security tokens), lists the following key advantages of this asset class in his article The Security Token Thesis.
- 24/7 access to markets
- Equity ownership
- Fast execution of transactions
- Reduced transaction costs
- Increase of market liquidity
- Possibility to automate compliance procedures
- Facilitation of exchange/trading operations with such assets
- Possibility to create an ecosystem of connected services.
How can we define if an asset is a security token?
Traditionally, the SEC’s position on what constitutes a security has been crucial. To understand the approach taken by the US financial regulator, one must go back to 1946 in Florida, where a company called the Howey Company, which owned orange plantations, offered investors an unusual solution. The scheme involved investors purchasing a plot of land with a plantation and the Howey Company making an explicit commitment to work there and pay them a portion of the proceeds.
The transaction, however, was stymied by the SEC, which determined that the scheme was an investment contract and that the participants should have been adequately protected. Howey Company appealed the decision, claiming that it was only a land sale. The case was heard by the United States Supreme Court, which sided with the Commission, launching the definition of what constitutes a security.
The Howey Test was created in honor of the company that got into a legal dispute with the authorities, and it states that a transaction is classified as a security if the investor answers yes to all four questions:
- There is the fact of investing money.
- There is an expectation of profit.
- The money is invested in an ordinary enterprise.
Any profit and its size do not depend on the efforts of the investor, but on the efforts of the counterparty or third party (the promoter).
This is the SEC’s current test for ICOs and tokens, and if all of these questions are answered affirmatively, the investor will invest in investment (security) tokens.
What is Security Token Offering (STO)?
It is widely believed that Security Token Offering (STO) is the next evolutionary step after the Initial Coin Offering (ICO) boom, defining the vector of industry development towards a more regulated and transparent market. However, STO and ICO are two distinct mechanisms for attracting investments that are intended for different purposes.
First of all, STOs are supposed to issue digital assets in full compliance with the requirements of securities laws. This should provide a higher degree of investor protection and reduce regulatory risks for token issuers. Furthermore, STOs have a different target audience in that only professional (accredited) investors can participate in such an offering.
Under US law, this category includes people who meet at least one of the following requirements:
- Annual income of more than $200,000 per person or $300,000 for a married couple, maintained within the past two years and projected in the current year in which the person plans to make the investment;
- Net assets in excess of $1 million, excluding the value of real estate in which the person permanently resides;
- An organization that has more than $5 million in assets, such as a venture capital or endowment fund;
- A company whose members are all accredited investors.
Furthermore, there are numerous technical details that investors and organizers must be aware of in order to properly participate in a STO. When conducting STOs in the United States, issuers must specifically consider the Securities Act of 1933, specifically provisions D, A+, and S. They describe various scenarios in which businesses can provide securities (security tokens) to investors.
What are the cons of security tokens?
The cryptocurrency industry, particularly the ICO industry, is frequently viewed as a reincarnation of the “Wild West,” where the strongest have the right and the ability to pull off this or that scheme. As previously stated, STO removes the entire process from the gray area, but it also deprives the sector of previously enjoyed advantages.
High entry threshold. Because security token investments are only available to accredited investors, they exclude a sizable portion of the cryptocurrency community, including many law-abiding participants.
Higher costs for issuers. Despite lower transaction costs, launching a STO involves a significant amount of red tape. This means that lawyers and other professionals who contribute to a smooth launch will face higher costs. As a result of the high costs, STOs are better suited to companies in later stages of development (Round A and above).
In his work on security tokens, the aforementioned Anthony Pompliano suggests that when the intermediary is removed, the buyer and seller assume its functions. He emphasizes that the parties traditionally in charge of preparing marketing materials, attracting investors, ensuring a high level of regulatory compliance, and successfully closing the deal are not included in the transaction. This statement, however, can be contested; many businesses successfully develop their own marketing departments without outsourcing such issues.
What is the future of security tokens?
Although a few projects are still desperately attempting to keep their tokens from being classified as securities, the general trend is in that direction. There is no unambiguous answer to the question of whether this is good or bad.
On the one hand, the arrival of institutional investors, specifically accredited investors, has the potential to dramatically alter the industry’s landscape and provide a significant impetus for development. On the other hand, it is important to remember that security tokens are not the same as cryptocurrencies in the traditional sense. There is a sizable segment of the community that flatly refuses to accept the new rules of the game, proposing its own solutions based on the bitcoin blockchain and, not without reason, believing that the future lies in a truly distributed network with its powerful security mechanism in the form of the Proof-of-Work algorithm.
At the same time, we should not dismiss players who will continue to follow traditional ICO principles. They may relocate to other jurisdictions or alter the rules of the game, but in general, they will continue to provide investment opportunities to a broader range of users.
The trend, on the other hand, is clear, though the transition will be difficult. In addition to complying with financial regulators’ rules, the industry requires the necessary infrastructure to develop. And this may prove to be more difficult than simply purchasing bitcoin.


All Comments